What Is an Incident Management Process?
An incident management process is a structured set of procedures that IT teams follow to detect, log, investigate, and resolve unplanned disruptions to services or systems. The goal is straightforward: restore normal service operations as quickly as possible while minimizing the impact on business operations and end users.
In the ITIL (Information Technology Infrastructure Library) framework, incident management sits at the heart of IT service management. ITIL defines an incident as any unplanned interruption to an IT service or a reduction in its quality. This broad definition covers everything from a single user unable to access their email to a full-scale outage affecting thousands of customers.
Why does it matter? Because every minute of unresolved downtime has a cost: lost productivity, damaged customer trust, and in regulated industries, potential compliance exposure. A well-designed incident management process transforms reactive firefighting into a repeatable, measurable discipline that strengthens operational resilience over time.
Incident Management vs. Incident Response
These two terms are often used interchangeably, but they serve distinct purposes.
Key Differences
Incident management is an IT service management function. It focuses on restoring service continuity as fast as possible, regardless of the root cause. Speed and business impact drive every decision in this process.
Incident response, by contrast, is a cybersecurity function. It focuses on investigating, containing, and remediating security breaches or threats. Root cause analysis and evidence preservation take priority over speed of resolution.
When to Use Each Approach
Use incident management for operational IT issues: server failures, application crashes, network outages, and performance degradations. Use incident response for security events: data breaches, ransomware, unauthorized access, or suspicious activity. Many mature organizations run both functions in parallel, with clear escalation paths between them when an operational incident reveals a security dimension.
Incident Management Process Flow
A reliable incident management process follows a consistent sequence of steps. Skipping or compressing any stage tends to result in recurring incidents, unresolved root causes, and SLA breaches.
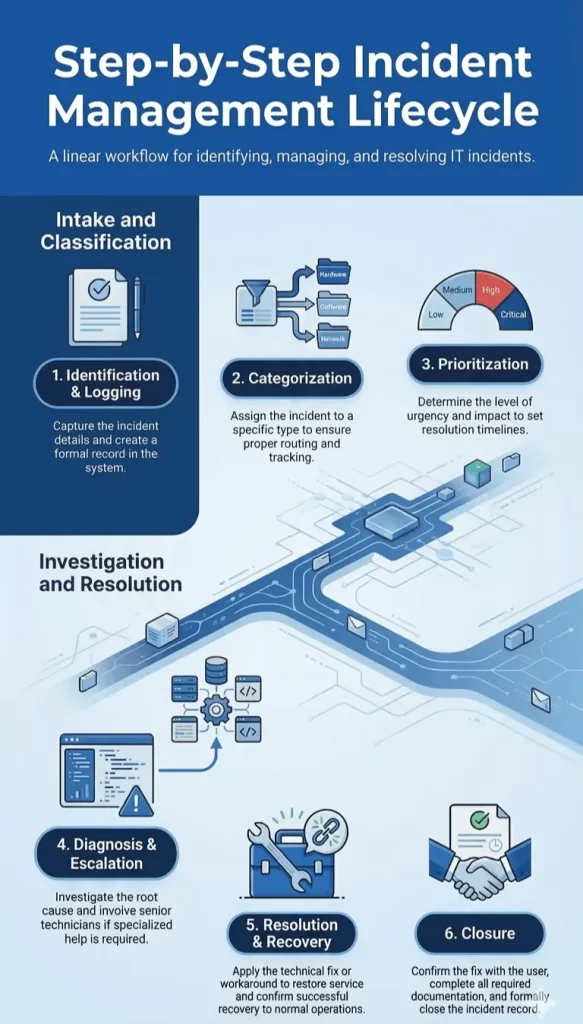
Step-by-Step Workflow
- Identification: An incident is detected through automated monitoring alerts, end-user reports, or proactive system checks. Early identification reduces resolution time significantly. AI-powered monitoring platforms can surface anomalies before users notice a degradation in service.
- Logging: Every incident is recorded in the IT service management system with full details: time of detection, affected systems, reported symptoms, and the user or alert that raised it. A complete log is the foundation for accurate reporting and post-incident review.
- Categorization: The incident is classified by type (hardware, software, network, security, etc.) and by the service or system it affects. Accurate categorization ensures the right team is assigned and helps identify recurring patterns over time.
- Prioritization: Priority is determined by two factors: urgency (how quickly resolution is needed) and impact (how many users or services are affected). This step drives SLA assignment and determines where the incident sits in the resolution queue.
- Diagnosis: The assigned team investigates the incident to identify its cause. This may involve reviewing logs, running diagnostics, reproducing the issue, or consulting knowledge base articles. The aim is a working resolution rather than a permanent fix at this stage.
- Escalation: When first-line support exhausts its resolution options within the defined timeframe, the incident escalates to a higher tier or a specialist team. Functional escalation moves the ticket to a more skilled team; hierarchical escalation brings in management when business impact is severe.
- Resolution: The incident is resolved and service is restored. The resolution is documented in full, including the steps taken, so it can inform future responses to similar incidents.
- Closure: The affected user confirms the issue is resolved, and the ticket is formally closed. The incident record is updated with final details and flagged for trend analysis or problem management review if the root cause warrants it.
Incident Severity and Priority Matrix
How Severity Is Defined
Severity reflects the technical impact of an incident on systems and services. Most organizations use a four-tier model:
- Severity 1 (Critical): Complete service outage affecting all users or core business operations.
- Severity 2 (High): Major functionality impaired, affecting a large number of users with a significant workaround required.
- Severity 3 (Medium): Partial degradation affecting a subset of users, with an available workaround.
- Severity 4 (Low): Minor issue with minimal business impact and a straightforward workaround.
SLA Mapping Examples
| Severity | Response Time | Resolution Target |
|---|---|---|
| Critical (S1) | 15 minutes | 4 hours |
| High (S2) | 30 minutes | 8 hours |
| Medium (S3) | 2 hours | 24 hours |
| Low (S4) | 8 hours | 72 hours |
SLA targets vary by organization and industry, but the principle remains consistent: higher severity demands faster response and tighter resolution windows.
Benefits of an Effective Incident Management Process
Reduced Downtime
A structured process eliminates the chaos of ad hoc responses. Teams know exactly what to do, who to escalate to, and how to document progress, which dramatically reduces mean time to resolution (MTTR).
Improved Customer Satisfaction
Users and customers experience faster resolutions and, where appropriate, timely communication about incident status. This transparency builds trust even during service disruptions.
SLA Compliance
With clear priority levels and response targets, teams can consistently meet the commitments defined in their service level agreements, protecting both client relationships and contractual obligations.
Operational Resilience
Over time, well-documented incident records feed into problem management, enabling root cause analysis and permanent fixes that reduce the frequency of recurring incidents.
Key Metrics and KPIs to Track
- Mean Time to Resolve (MTTR): The average time from incident detection to full resolution. This is the single most watched metric in incident management.
- Mean Time Between Failures (MTBF): The average time between recurring incidents on the same system or service. A rising MTBF signals improving stability; a falling one signals a deeper systemic issue requiring problem management attention.
- First Response Time: How quickly the service desk acknowledges and begins working on an incident after it is logged. This directly affects user perception and SLA compliance.
- SLA Compliance Rate: The percentage of incidents resolved within their defined SLA targets. Most organizations aim for 95% or above across all severity levels.
Incident Management Tools and Features to Look For
Core Capabilities
A capable incident management tool should provide a centralized ticketing system, automated alert ingestion from monitoring platforms, a configurable workflow engine, a searchable knowledge base, and real-time dashboards for queue visibility and SLA tracking.
Automation and AI Features
Modern platforms go well beyond basic ticketing. Look for auto-classification of incoming incidents based on historical patterns, intelligent routing to the right resolver group, AI-driven anomaly detection that raises incidents before users report them, and automated escalation triggers when SLA thresholds approach breach.
Integration Requirements
An incident management tool should connect seamlessly with your monitoring and observability stack, your CMDB, your communication platforms (Slack, Microsoft Teams), and your change and problem management modules. Siloed tools create information gaps that slow down resolution.

Industry Use Cases
BFSI (Banking, Financial Services, and Insurance)
In financial services, even minutes of downtime during trading hours or payment processing carries significant monetary and regulatory consequences. Incident management in BFSI environments must align tightly with compliance frameworks and deliver audit-ready records of every resolution step.
Telecom
Telecom providers manage vast, interdependent infrastructure where a single node failure can cascade across services. Automated incident detection, rapid escalation paths, and real-time customer impact analysis are essential capabilities in this sector.
Government and Public Sector
Government IT teams support critical citizen services where availability and data integrity are paramount. Incident management processes in this sector typically incorporate strict change controls, multi-tier approval workflows, and compliance with local data sovereignty requirements.
Oil and Gas (Middle East)
In the Middle East’s energy sector, operational technology (OT) and IT systems increasingly converge. Incident management must span both environments, with fast response capabilities for field operations, remote monitoring of distributed assets, and integration with safety management systems.
Emerging Trends in Incident Management
- AI-driven incident response: AI is moving from alert correlation to active recommendation. Modern platforms analyze incident patterns, suggest probable causes, and in some cases trigger automated remediation, cutting resolution times by a significant margin.
- AIOps: AIOps platforms layer machine learning across the entire IT operations stack, reducing alert noise, identifying root causes faster, and enabling IT teams to shift from reactive to predictive operations.
- ChatOps: Teams are integrating incident workflows directly into collaboration tools like Slack and Microsoft Teams. Responders can acknowledge, update, and resolve incidents without leaving their communication platform, reducing context-switching and improving response speed.
- SRE practices: Site Reliability Engineering principles are influencing how organizations define error budgets, set service level objectives (SLOs), and treat toil reduction as a first-class engineering priority alongside incident resolution.
How Infraon Enhances Incident Management
Infraon brings together the core capabilities of a mature incident management platform with AI-driven intelligence, making it particularly well-suited for enterprises managing complex, distributed IT environments across the UAE and broader Middle East.
- Automation: Infraon automates incident classification, routing, and escalation based on configurable rules and AI recommendations, reducing manual handling and accelerating time to resolution.
- SLA Tracking: Real-time SLA dashboards give teams full visibility into breach risks before they occur. Automated alerts trigger when incidents approach their resolution targets, enabling proactive intervention.
- AI Insights: Infraon’s AI engine correlates incidents across the environment to surface patterns, identify probable root causes, and recommend resolutions based on historical data, turning every resolved incident into institutional knowledge.
- Multi-Region Support: For organizations operating across multiple geographies, Infraon supports multi-region deployment with localized compliance configurations, ensuring data residency and regulatory requirements are met at every location.