70-80% of network outages are caused by manual configuration errors and unauthorized changes
Solution
Automated change validation, approval workflows, and test-based systems, reducing configuration errors by 90%
Loved by 25 million+ users
Network configuration automation reduces ACL deployment from days to minutes with zero unauthorized changes.
Prevent $1M-$5M compliance audit failures with intelligent NCCM software designed for enterprise-scale network operations.
Transform network configuration and change management from manual processes to intelligent automation.
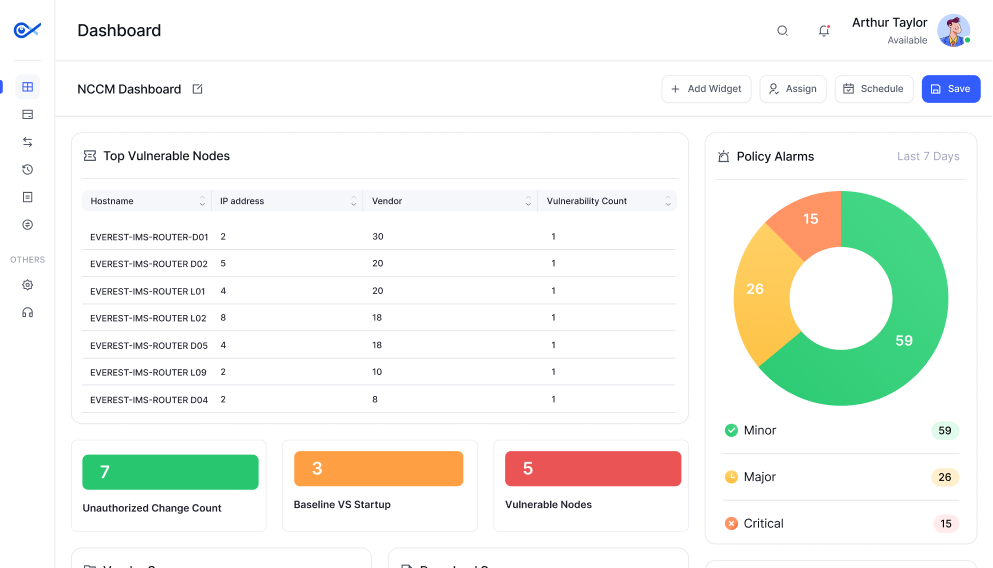
One comprehensive NCCM solution automating configuration backups, change workflows, compliance validation, and vulnerability assessment across 15,000+ multi-vendor devices.

Most enterprises struggle with 70-80% of network outages caused by manual configuration errors. They face 3-5 days required to deploy ACL changes across multi-site networks, and $1M-$5M annual compliance audit failure costs.
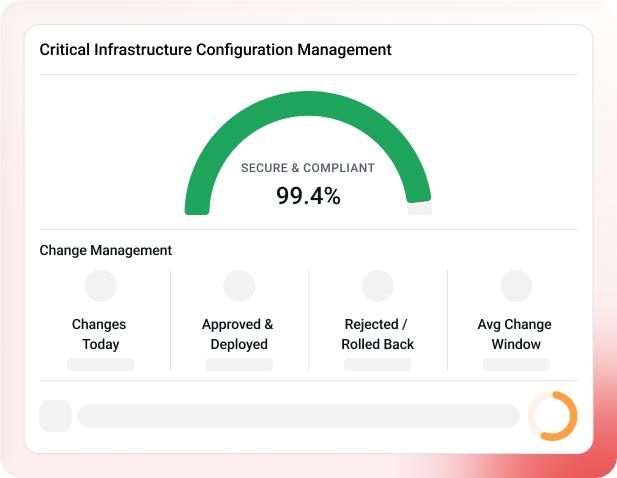
Infraon NCCM software automates critical workflows, eliminating configuration drift, security vulnerabilities, and compliance failures through intelligent automation. Here's how our network configuration and change management solution reduces ACL configuration from days to minutes while ensuring regulatory compliance.

Automate RBI compliance reporting across 15,000+ devices with complete audit trails tracking configuration changes, policy violations, and regulatory adherence for banking infrastructure.
Reduce ACL and NAC configuration from days to minutes across 10,000 branches, handling Cisco, Juniper, HP, Palo Alto, and Fortinet devices through single-touch deployment.
Restrict unauthorized access through approval workflows, secure the CLI with session recording and real-time vulnerability assessment, and protect distributed branch networks.
Manual network configuration creates operational risk that increases as infrastructure scales. Here's what Infraon network configuration and change management software fixes immediately.
70-80% of network outages are caused by manual configuration errors and unauthorized changes
Solution
Automated change validation, approval workflows, and test-based systems, reducing configuration errors by 90%
3-5 days average time deploying ACL or firewall rule changes across multi-site networks
Solution
Bulk configuration deployment pushing modifications to hundreds of devices simultaneously, reducing deployment from days to minutes
$1M-$5M annual cost of compliance audit failures due to configuration drift
Solution
Continuous compliance scanning against RBI, PCI-DSS, SOX, HIPAA policies with automated reporting, ensuring zero audit findings
60% of network devices have outdated configurations violating security policies
Solution
Real-time configuration drift detection with automated remediation workflows, ensuring all devices match approved baselines
15-20 hours/week that network engineers spend on manual configuration and documentation
Solution
Automated configuration backups, change workflows, and audit trail generation, freeing 1-2 FTE worth of engineering time
Regulatory compliance pressure requiring strict configuration management and audit trails
Solution
RBI, PCI-DSS, SOX, HIPAA compliance templates with pre-built policies and auditor-ready reports
When network engineers, security officers, and IT administrators work in the same network configuration and change management tool, collaboration becomes automatic.
Automated configuration backups with version control and timestamps, enabling one-click rollback capability.
Change automation deploying ACL changes across hundreds of devices in minutes with approval workflows.
Compliance validation providing continuous checking with instant violation alerts and pre-built audit reports.
Configuration drift detection, identifying unauthorized changes in real-time with complete attribution tracking.
Vulnerability assessment scanning configurations for weaknesses with automated remediation workflows.
Secure CLI access providing centralized device access with session recording and complete audit trails.
Infraon NCCM software automates device configuration, compliance validation, vulnerability assessment, and change workflows into a unified solution. Intelligent automation capabilities deliver enterprise-scale network configuration and change management.
One tool combining automated backups, change workflows, compliance validation, drift detection, vulnerability assessment, and secure CLI access, managing 15,000+ multi-vendor devices.
Fast implementation with automated discovery, pre-configured compliance templates, getting teams productive in 1-2 weeks versus 4-6 weeks with competitive solutions.
Dedicated technical engineers supporting RBI, PCI-DSS, SOX, HIPAA compliance workflows, not outsourced call centers reading scripts.
Verified feedback from enterprises that transformed network operations with Infraon network configuration and change management software.




















Choosing the right network configuration management software determines whether you achieve automated compliance or continue struggling with manual processes costing $1M-$5M annually. This comprehensive checklist covers must-have automation features, regulatory compliance requirements (RBI, PCI-DSS, SOX, HIPAA), and implementation best practices for banking, energy, healthcare, manufacturing, and MSP sectors.
Download Your Free Guide