Investments in advanced technology and superior assets are made for a reason, that is, better products and service delivery, all to retain their market position in times of digital transformation. However, getting a solid ROI will prove that the investments were worth including in your budget. Getting the expected returns will mean that each asset demonstrates its worth, achievable only through optimizing asset usage. And the first step towards managing your assets is accurate inventory and asset discovery. That’s where ITAM comes in.
What is ITAM?

IT asset management (ITAM) involves cataloging, tracking, and maintaining an enterprise’s technology assets. ITAM combines the tracking capability and analysis of the contractual and financial elements against actual inventory to drive service delivery success. Assets in any enterprise can include tangible, physical assets like networks, hardware, and servers, or intangible assets like software applications, licenses, purchase orders, and SLAs.
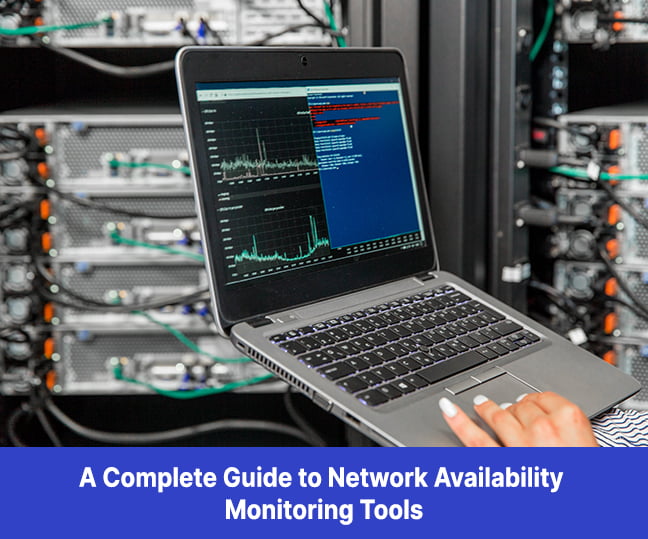
ITAM has a framework to document and manage the lifecycle of every IT asset. It runs the gamut from requisitions and purchasing to its retirement or disposal. The traditional approach involved manually filling data in spreadsheets, which was labor-intensive and time-consuming. Thankfully, the old ways have been replaced with ITAM solutions that help align your hardware and software inventory, asset owners and users, and asset location information in a centralized dashboard. Monitoring assets is central to ITAM solutions as they lead to the discovery of all relevant information on your assets. There are two ways IT assets can be monitored – agent-based and agentless. Understanding both methods can help you choose the one best suited for your unique business needs.
What is agent-based asset discovery?
Agent-based IT asset monitoring requires installing one or more instances of agent software on each target system. The agents help collect performance and availability metrics from servers, laptops, desktops, VMs, operating systems, middleware, and network devices. These agents also collect data on software applications and then transmit the data to a central monitoring system, such as a hub, collector, controller, server, etc. Agents consist of physically going to the target machine and installing the agent or performing a remote installation through SSH (for Linux machines), RPC, SMB (for Windows machines), etc.
You may also install some agents using automated mass deployment technology that will work with a few monitoring solutions.
When the agents reside on target systems, they can collect data on service availability, network usage, CPU performance, file systems usage, RAM, and other metrics that offer deep insights for root cause analysis and troubleshooting. You can also use builder tools to customize the agents to enhance the capabilities of each agent instance by adding custom scenarios, metrics, and queries.
What is agentless asset management?
In simple terms, an agentless IT monitoring tool doesn’t need any agent software to perform monitoring. These monitoring tools collect metrics by leveraging APIs using management protocols or specifications like the Windows Management Instrumentation (WMI), Simple Network Management Protocol (SNMP), or Common Information Model (CIM).
Agentless monitoring solutions don’t have deployment and maintenance issues but are faster and easier to implement. However, agentless IT monitoring tools can’t compete against the breadth and depth of metrics of agent-based solutions.
Agentless monitors come with more significant network overhead because the monitoring activities are carried out over the network. Their over-dependence on the network makes agentless solutions more vulnerable to network issues, and packet loss, latency, and poor network conditions have a negative impact on reliability. However, they can offer greater functionality and extensibility to the monitoring solution. But they have downsides. They involve a manual deployment and can be time-consuming. Agentless solutions can be challenging for larger enterprises across different geographies and become an issue for privacy and security.
Knowing the difference between agent-based and agentless asset monitoring solutions is one thing. But, it is more important to know when to use either in an enterprise.
When to use agent-based IT monitoring?
Suppose you have poor network quality or availability issues; you would need an agent-based monitoring solution as it is not dependent on your network. You don’t even need a network connection. Therefore, agent-based solutions are perfect for monitoring your IT assets in this situation. They also effectively monitor endpoints in remote locations or disconnected from the corporate network. Furthermore, they offer greater visibility and in-depth analysis with minimal deployment and maintenance costs.
When to use agentless IT monitoring?
An agentless monitoring tool is ideal if you cannot install an agent in a target system. Some examples include printers, routers, switches, etc., that do not allow asset monitoring tools. You may also find agentless monitoring tools useful if you don’t have enough resources to deploy or manage the solution. Other scenarios where agentless monitoring works better are when you need only basic inventory data and performance metrics or when you need to monitor legacy systems. Also, smaller enterprises may not want to deal with privacy or security issues and may opt for an agentless monitoring tool.
Agent-based vs. agentless discovery
To help you decide between Agent-based vs. Agentless Discovery methods, we have listed the differences below:
Deployment
Agent-based discovery requires installations on a target system. It may be a challenge for large enterprises and in remote geographical locations. Agentless monitoring tools don’t need any installations.
Breadth and depth of metrics
Agent-based discovery can cover broader metrics and provide more insights into your IT assets’ inventory and performance. Agentless monitoring can only cover a lesser range of metrics, thereby having fewer insights into your IT assets.
Resource overheads
Agent-based methods use computing resources on the target system, impacting the performance where resources were a limited option and if you have legacy systems. Agentless monitoring requires no target systems, nor does it need additional resources.
Network overheads
Agent-based discovery tools use minimal network bandwidth, whereas agentless monitoring uses more bandwidth.
Maintenance
Agent-based may need monitoring, occasional patching, and troubleshooting of agents on target systems. However, an agentless discovery tool doesn’t need any such maintenance.
Extendability
The best advantage of an agent-based discovery is that the agents offer customization and extendability, whereas there is no such capability in an agentless discovery.
While there are a few differences between agent-based and agentless monitoring, there are other methods to consider, like the active and passive asset discovery methods.
Active asset vs. passive asset discovery tool
The active asset discovery method is standard and uses software covering all devices connected to the network. It can also discover those assets that try to log into devices to get an inventory of all connected applications. Unlike an active asset discovery method, the passive asset discovery tool locates all services that run on the network by monitoring the traffic from clients and servers.
In conclusion
Enterprises rely on their IT assets to manage their operations, and losing track of any asset will likely impact the ROI. Clearly, they need a streamlined and accurate way to monitor and manage their assets to get the most out of their inventory. Choosing an asset-based or agentless monitoring system can significantly protect your assets and ensure that they are used optimally.