Every computer network relies on network devices to stay connected, secure, and efficient. These devices are the building blocks that make communication possible between systems, users, and applications. From small home setups to large enterprise data centers, understanding how different devices work helps IT teams design networks that are fast, reliable, and secure.
In this blog, we will explain what network devices are, their core functions, the different types of networking devices, and how they are used in real-world IT environments.
What Are Network Devices?
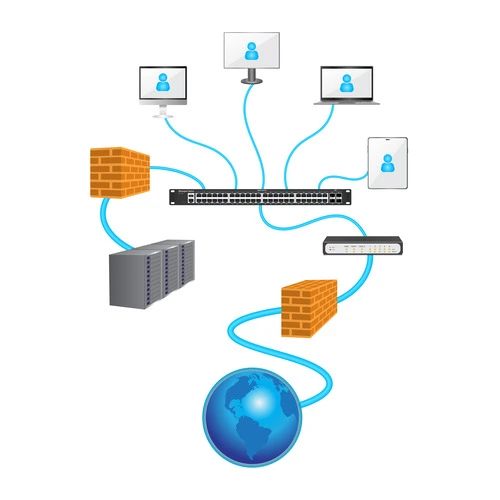
Network devices (also called networking devices or network components) are hardware or software elements that make it possible for data to move within and across networks. They enable routing, filtering, transmission, and security of data.
These devices can be physical, like routers or switches, or virtual, like cloud-based firewalls and software-defined routers. Every IT setup, whether in homes, enterprises, or data centers, depends on a mix of these devices to ensure smooth communication.
Functions and Uses of Networking Components
The main uses of networking devices include:
- Allowing communication across local (LAN) and wide (WAN) networks
- Managing and controlling data traffic to avoid congestion
- Boosting the speed, security, and reliability of data exchange
- Supporting scalability, segmentation, and connectivity in the ever-evolving IT sector.
From connecting employees in offices to powering cloud-based services, networking devices are critical to modern digital operations.
Related Blog: Network Topologies in Computer Networks
Common Types of Networking Devices and Their Functions
1. Repeater
A repeater strengthens and regenerates signals over long distances, preventing signal loss in large networks.
2. Hub
A simple device that broadcasts data to every connected device is a hub. It is being replaced by switches in modern setups, as it lacks intelligence.
3. Bridge
A bridge connects two LANs to form a larger network. It filters traffic and reduces collisions, improving efficiency.
4. Switch
Switches are smarter than hubs. They forward data only to the intended recipient and support full-duplex communication. This reduces traffic and improves performance.
5. Router
A router connects multiple networks and directs data packets based on IP addresses. It is essential for internet connectivity.
6. Gateway
It allows communication between networks that use different protocols or systems.
7. Brouter
A brouter combines the functions of a bridge and a router, handling both routable and non-routable protocols.
8. Network Interface Card (NIC)
A hardware component that connects a device to a network can be explained as a NIC. It can be wired or wireless.
9. Modem
A modem converts digital signals to analog (and vice versa). It enables internet access over phone or cable lines.
10. Wireless Access Point (WAP)
A WAP allows wireless devices to connect to a wired network. This expands mobility and flexibility.
Additional Network Components
Network Cables
Physical media such as Ethernet, coaxial, and fiber optic cables form the backbone of data transmission.
Transmission Media, Protocols, and Topology
These are essential network components that define how data moves, how devices communicate, and how networks are structured.
Virtual Network Components
In addition to physical devices, virtual devices like software-based routers, firewalls, and switches are now common in cloud and hybrid environments. Some of its benefits are flexibility, scalability, and cost efficiency. It is one of the best choices for modern enterprises.
Common Challenges in Network Device Management
Managing network devices can come with challenges such as

- Connectivity issues due to faulty cables or ports
- Hardware malfunctions leading to downtime
- DNS misconfigurations are disrupting access
- Overutilization or power fluctuations affecting performance
- Environmental issues like overheating due to poor ventilation
Best Practices for Managing and Securing Networking Devices
To keep networks reliable and secure, IT teams should:
- Regularly update device software and firmware
- Harden devices against unauthorized access
- Use VLANs to segment networks for better security
- Continuously monitor traffic and set alerts for anomalies
- Apply role-based access and strong user controls
- Document configurations and perform periodic audits
Companies like Infraon simplify these tasks by providing unified monitoring, control, and automation for both physical and virtual network Components.
Your Top Network Devices Guide for Efficient Connectivity
A slow network feels like rush hour traffic that never ends. Files take minutes to open, video calls freeze at the worst moments, and new applications crawl. This daily friction often points back to the hardware directing your data behind the scenes.
The routers, switches, and firewalls you choose determine if your network is a bottleneck or a backbone.
Therefore, getting the right devices in place is the first step. Knowing how to manage them together is what turns a collection of hardware into a reliable, high-performance system.
How Modern Network Devices Compare Across Performance and Use Cases
Network hardware has evolved from simple connectivity boxes to intelligent, application-aware systems. The difference lies in control, visibility, and adaptability to modern demands.
Unmanaged vs. managed devices
Basic, unmanaged switches and hubs work immediately after you plug them in. They are fixed in their operation, which makes them simple and low-cost for very small, static setups where no configuration is needed.
Managed devices provide control. You can configure ports, set up virtual networks (VLANs), prioritize critical traffic, and monitor performance. This flexibility is essential for any business network that needs to grow, adapt, and remain secure.
Traditional hardware vs. software-defined networking
In a traditional network, each device is configured individually. Changing a security policy or rerouting traffic often requires touching multiple boxes, which is slow and prone to error.
Software-Defined Networking (SDN) centralizes control. A software controller manages the entire network’s behavior, empowering you to make network-wide changes instantly through a single interface.
This approach is key for dynamic environments like cloud data centers or campuses with shifting connectivity needs.
Why Centralized Monitoring Makes Network Devices Easier to Manage
As networks grow, device counts multiply. You might have routers from one vendor, switches from another, and firewalls from a third. Each has its own management console, log format, and alert system. Manually checking each one is not just time-consuming; it’s ineffective.
- Unified visibility: A centralized platform provides a single dashboard showing the status of every device, regardless of type or vendor.
- Faster troubleshooting: When an issue arises, you can trace a connection path across routers and switches in seconds instead of hours.
- Proactive maintenance: Performance trends and early warning signs like rising error rates or temperature alerts become visible before users are affected.
- Consistent policy enforcement: You can ensure security and configuration policies are applied uniformly across all managed devices from one control point.
Without this unified view, IT teams are left reacting to problems instead of preventing them, and network reliability becomes a constant challenge.
How Infraon ITIM Helps You Track and Manage All Your Network Devices
Managing a diverse network requires more than periodic check-ups. It requires continuous, automated oversight. Infraon ITIM (IT Infrastructure Monitoring) provides this oversight by unifying discovery, monitoring, and management in one platform.
Automatic discovery and mapping
Infraon ITIM automatically discovers every device on your network, from core routers to edge switches. It builds an interactive, real-time map that shows how devices are connected, giving you an immediate understanding of your network’s topology.
Health and performance monitoring
Infraon ITIM continuously monitors key health metrics for each device:
- CPU and memory utilization
- Interface status and traffic loads
- Temperature and hardware health
- Key performance indicators (KPIs)
It triggers threshold-based alerts that notify your team of potential issues before they impact service, enabling proactive intervention.
Compliance and configuration backup
Infraon ITIM helps maintain network integrity by tracking configuration changes and automating backups. You can define compliance policies to ensure device configurations adhere to security standards, reducing risk and audit preparation time.
Trends That Will Shape the Future of Network Devices
The next generation of networking is being defined by intelligence, automation, and cloud-native management.
AI-driven optimization and predictive operations
Artificial intelligence is moving into network operations. AI can analyze traffic patterns to predict congestion and automatically reroute data. It can also identify the root cause of performance issues by correlating data across devices, drastically reducing mean time to repair (MTTR).
Zero-trust security models embedded in hardware
The zero-trust principle of “never trust, always verify” is becoming a hardware requirement. Newer firewalls and switches have built-in capabilities to authenticate every device and user attempting to access the network, segment traffic micro-segments, and enforce strict access policies at the port level.
The rise of cloud-managed networks
Management itself is shifting to the cloud. Cloud-managed network solutions equip administrators to configure, monitor, and secure globally distributed devices from a single web portal. This simplifies operations for branch offices and remote sites, enabling consistent policy deployment everywhere.
Ready to Improve Visibility Across All Your Network Devices?
Managing a modern network doesn’t have to mean managing complexity. With the right approach and tools, you can transform your network infrastructure from a source of problems into a platform for growth.
Start by gaining a complete, real-time view of every device in your ecosystem. See how automated monitoring and intelligent alerts can free your team from reactive firefighting.
Explore how Infraon ITIM provides unified visibility and control across your entire network infrastructure.
Conclusion
Networking devices play a critical role in ensuring secure and reliable communication across IT infrastructures. From simple repeaters to advanced virtual devices, each has a unique function in supporting connectivity, scalability, and performance.
Organizations that invest in understanding and maintaining these network components are better equipped to avoid downtime, strengthen security, and enable smooth digital operations. Reviewing your current setup and upgrading where necessary is the first step toward building a future-ready network.
FAQ Section
Q1. What are networking components in simple terms?
They are hardware or software components that connect computers and systems, allowing data to be transmitted securely and efficiently.
Q2. What are the main types of networking devices?
Common types include repeaters, hubs, bridges, switches, routers, gateways, brouters, NICs, modems, and wireless access points.
Q3. What is the difference between a router and a switch?
A switch connects devices within a single network and directs traffic efficiently, while a router connects multiple networks and determines the best path for data to travel.
Q4. What are virtual networking components, and how are they used?
They are software-based versions of physical devices, used in cloud and hybrid environments for flexibility, scalability, and cost savings.
Q5. How can I secure my networking components from cyber threats?
Apply regular updates, use strong access controls, monitor network traffic, segment networks, and follow security best practices to reduce risks.
Q6. What’s the easiest way to manage a large network with multiple device types?
The easiest way is to implement a centralized network monitoring and management platform. This type of tool automatically discovers all devices, provides a unified health dashboard, and allows for consistent configuration and policy management from a single interface, eliminating the need to juggle multiple vendor-specific consoles.
Q7. How do I know if my network devices need an upgrade?
Key signs include consistent performance degradation (slow speeds, high latency), an inability to support new security protocols, lack of compatibility with modern software-defined features, and frequent hardware failures. Additionally, if devices are no longer receiving security updates from the vendor, they pose a significant risk and should be replaced.